Blog
Best Ethical Hacking Course in Pune, India [2025]
- September 29, 2021
- Posted by: Sangeeta
- Category: ethical hacking

Table of Contents
Ethical Hacking Course in Pune
In today’s world, where cybersecurity threats are prevalent, many organizations are turning to ethical hacking to protect themselves. As a result, individuals are enrolling in ethical hacking courses to help combat cybercriminals and secure online spaces. If you live in Pune and want to start a career in this exciting field, this article is for you. It will explain why learning ethical hacking is important and why Pune is a great place to begin your journey.
What is an Ethical Hacking Course?
Ethical hacking, or “white-hat hacking,” involves skilled people. They find and report security weaknesses in computer systems, networks, and applications with permission. These hackers use their expertise to enhance technology and protect organizations. By mimicking the tactics of harmful hackers, they find security gaps. They fix these gaps before real threats can take advantage of them. Unlike black-hat hackers, ethical hackers do not break security for bad reasons. They work to protect information systems. They are dedicated to keeping their clients safe.
Why Choose an Ethical Hacking Course in Pune?
The rise in cyber attacks has made companies seek workers skilled in ethical hacking. They want to protect their information technology. Today, ethical hackers do more than protect companies. They are vital for keeping personal information safe and securing our nation.
This is a clear indication that everyone should enroll in an ethical hacking course:
- A Rapidly Expanding Need for Cybersecurity: Threats to information systems are inevitable in this age, and businesses are seeking skilled people to contain the threat and defend the enhanced security system. Ethical hacking professionals are increasingly in high demand in this field of cybersecurity.
- Well-Paying Career Choice: There is a great need for and appreciation of professional, ethical hacking, and cybersecurity expertise, which explains the salaries. The median annual salaries of an ethical hacker are appealing.
- Range of Options to Choose From: Depending on a person’s specialties, ethical hackers can be penetration testers, security analysts, security consultants, and network security specialists, among others. The moment you have learned ethical hacking, the end to opportunities has not come.
- Incessant Education: Once again, developments in the attack against very strong information systems defined as such by the users and ethical hackers come about, and therefore, ethical hackers need to adapt to such changes. As such an operation is satisfying for people who crave action and sleepless days, it makes ethical hacking an enticing profession.
Why choose Pune for its ethical hacking course?
Pune is becoming one of the fastest-growing cities in terms of economic development and one of the potential centers for ethical hacking training. Here’s why:
- Booming IT Sector: Thanks to many IT corporations and startups, the city of Pune provides a great IT ecosystem and will continue growing. This means even more scope for internships, networking, and job placements.
- Expert Faculty and Institutions: In Pune, some of the best institutions provide complete ethical hacking courses. These institutes offer practical training, qualified teachers, and timetables by the latest trends, which help you gain the required skill set.
- Affordable Education: Though cities like Bangalore or Delhi are ideal for pursuing IT-related activities, the overall cost of quality education in Pune is lower. This gives students a cheaper alternative route to acquire critical technical know-how.
Ethical Hacking Training Institute in Pune
- Bytecode: Course Overview & Benefits
Institution A, renowned for its advanced curriculum, covers essential areas of ethical hacking in-depth. With a team of seasoned professionals as trainers and a state-of-the-art lab setup, it promises a hands-on experience like no other. Graduates often praise the institution for its real-world simulation exercises and post-course support. - Craw Security: Course Highlights & Success Stories
Institution B stands out for its focus on both conventional and emerging threats. Their advanced modules on AI-driven threats and cloud vulnerabilities prepare students for future challenges. Alumni of Institution B hold prominent positions in top tech companies worldwide, a testament to its quality training. - Crawsec: Why It Makes the Cut
While Institution C is relatively new to the scene, its modern approach to ethical hacking education has quickly gained traction. The course is tailored to meet industry needs, ensuring that students are job-ready from day one. Additionally, its association with international ethical hacking communities offers students global exposure. - Symbiosis Centre for Information Technology (SCIT):
SCIT, located in Pune, is known for its information technology management programs. While they may not explicitly offer ethical hacking courses, they might have cybersecurity-related courses or collaborations with organizations that provide such training. - QuickHeal Academy:
QuickHeal, a well-known cybersecurity company, has an academy that offers training programs in cybersecurity. They might have courses or workshops related to ethical hacking. It’s worth checking their website or contacting them for details. - SEED Infotech:
SEED Infotech is a prominent IT training institute with a presence in Pune. They offer various courses in information technology and cybersecurity. Check if they provide ethical hacking courses or related certifications. - i-Secure Labs:
i-Secure Labs is a cybersecurity training institute that may offer ethical hacking courses. They might have workshops, certifications, or an ethical hacking course in Pune. - Local Universities and Colleges:
Check with universities and colleges in Pune, such as Pune University or colleges offering IT and computer science courses. Some educational institutions collaborate with cybersecurity training providers to offer specialized courses. - Online Platforms:
Explore online platforms like Craw Security and Coursera for ethical hacking courses. While not specific to Pune, these platforms offer flexibility in learning and might be a good option.
What Can You Expect from an Ethical Hacking Course in Pune?
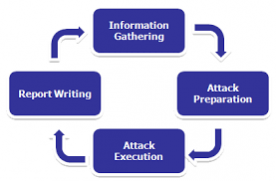
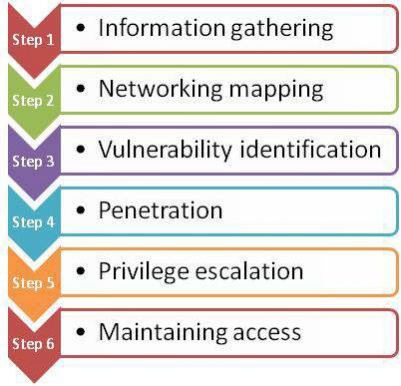
The majority of these courses most often include both theoretical information as well as practical exercises and activities. Here’s a list of topics that you will come across:
- Introduction to Ethical Hacking: Gain awareness of basic information security concepts, hacking methods and activities, and the need for ethical hacking.
- Networking & Security Basics: Understanding network architecture, firewalls, devices, and methods used for data protection against cyberattacks.
- Vulnerability Assessment: Learn about the criteria for conducting proper vulnerability assessments to ascertain the weak points in the systems and networks.
- Penetration Testing: Participate actively in penetration testing by performing various hands-on exercises using various tools.
- Understanding Cyber Laws: There are some legal considerations that every ethical hacker must abide by. You will find out about the cyber laws enacted concerning ethical hacking.
- Tools & Techniques: Get familiar with the most used ethical hacking tools, including Kali Linux, Metasploit, Wireshark, and Nmap.
In summary
How might this report be extended in future work? Further research can be done on implementing accurate and fast logging-in applications other than web-based systems set to connect remotely to the central system and provide a working identifier for each individual who connects remotely. If you would love such possibilities where your skill can be used in combating cyber criminality, more so against children, then registering for an ethical hacking course in Pune is extremely advisable.
FAQ about Ethical Hacking
- What ethical hacking course is right for me?
It depends on your learning preferences and objectives, which ethical hacking training program would be the most effective. Some of the top certifications include Certified Ethical Hacker (CEH), Offensive Security Certified Professional (OSCP), and EC-Council Certified Security Analyst (ECSA). They provide advanced knowledge along with practical training on different cybersecurity measures and tools.
- How much does an ethical hacking course typically cost?
The cost of various ethical hacking courses differs depending on the provider, level of the material, and the type of certification. For instance, most of the entry-level courses will range from Rs 20000 to Rs 50000. This is, however, not true for the advanced level, such as CEH or OSCP certification, which can start from Rs 50000 to Rs 150000 and above.
- What is the pay of an ethical hacker?
In as much as it is a financially rewarding profession, the pay of an ethical hacker depends on one’s experience, certifications, and current location. In India, even entry-level ethical hacking experts can expect to earn anywhere between Rs 3 to 6 lakhs per annum. With advanced certifications and experience, that amount can go as high as 10 to 20 lakhs and some more per annum. Outside India, however, it is worse; However, the ethical hacking profession is more rewarding concerning the remuneration and more experienced engineers earn more.
- Which college is best for ethical hacking in Maharashtra?
In Maharashtra, some of the best colleges offering cybersecurity and ethical hacking courses include Symbiosis Institute of Computer Studies and Research (SICSR) and MIT Pune and IIT Bombay, offering courses on cybersecurity in specialization.
- Which language is best for hacking?
In hacking, programming languages such as Python, JavaScript, C, C++, and Ruby are especially employed. And since the programming is easy, a lot is done using libraries within the language when it comes to Cybersecurity in relation to Python programming. JavaScript is crucial for web hacking, whereas C and C++ are beneficial in handling the low-level parts of the system.
- Is ethical hacking a good career?
Yes, ethical hacking is a very bright career option now and in the future, as cybersecurity is more and more important. Now, with companies trying to keep all their confidential information and systems safe, the trend for ethical hacking is quite in, meaning good salaries and growth in careers.
- What is the maximum age limit for attending an ethical hacking course in Pune?
There is no age limit mentioned for existing courses on ethical hacking in Pune. However, several of the institutions might be comfortable with candidates who are eighteen years and above. The main requirement is having a good knowledge of computers and network systems.
- Which branch is proficient in striking the moral code to be known as an ethical hacker?
The most relevant education for ethical hacking is in computer science, information technology, or cybersecurity. These branches build a good basis in programming, networking, and system security, which are necessary in the career of an ethical hacker.
- Which certificate is compulsory for ethical hackers in Pune?
The Certified Ethical Hacker (CEH) certification is the most requested and pursued in ethical hacking. Some others include Offensive Security Certified Professional (OSCP) and the EC-Council’s Certified Security Analyst (ECSA).
- Which examination will be the most difficult to pass in hacking?
The Offensive Security Certified Professional (OSCP) exam is always regarded as the most difficult examination in the world of ethical hacking. It pushes one to acquire practical penetration skills along with practical time management skills as much as one has to accomplish a given task within a limited time.
- Is there an examination in this area of cyber security called ethical hacking?
Yes, there are several examinations for ethical hacking certificates. The most popular excavator is the CEH (Certified Ethical Hacker) exam, EC-Council. Other worthy examples include OSCP (Offensive Security Certified Professional) and CompTIA PenTest+.
- How much will it cost to take the CEH examination?
The CEH (Certified Ethical Hacker) exam costs approximately $1199, depending on the country and training provider. Some of the institutions may include a prove package of the course plus the fee for the examination.
Related
Leave a ReplyCancel reply
About Us
CrawSec, commonly known as Craw Security is a paramount cybersecurity training institution situated at Saket and Laxmi Nagar locations in New Delhi. It offers world-class job-oriented cybersecurity training programs to interested students.
Contact Us
1st Floor, Plot no. 4, Lane no. 2, Kehar Singh Estate Westend Marg, Behind Saket Metro Station Saidulajab New Delhi – 110030
+91 951 380 5401
training@craw.in
HR Email : HR@craw.in
Trending Cyber Security Courses
One Year Cyber Security Course | Basic Networking with AI | Linux Essential | Python Programming | Ethical Hacking | Penetration Testing with AI | Cyber Forensics Investigation | Web Application Security with AI | Mobile Application Security with AI | AWS Security with AI | AWS Associate with AI | Red Hat RHCE | Red Hat RHCSA | Red Hat Open Stack | Red Hat RH358 | Red Hat Rapid Track | Red Hat OpenShift | CCNA 200-301 | CCNP Security 350-701 | CompTIA N+ | CompTIA Security+ | CompTIA Pentest+ | CompTIA A+ | CompTIA Cysa+ | CompTIA CASP+ | Pen-200 / OSCP | Pen-210 / OSWP | Reverse Engineering | Malware Analysis | Threat Hunting | CRTP | CISA | Certified Ethical Hacker(CEH) v13 AI | Certified Network Defender | Certified Secure Computer User | Eccouncil CPENT | Eccouncil CTIA | Eccouncil CHFI v11
Are you located in any of these areas
NARELA | BURARI | TIMARPUR | ADARSH NAGAR | BADLI | RITHALA | BAWANA | MUNDKA | KIRARI | SULTANPUR MAJRA | NANGLOI JAT | MANGOL PURI | ROHINI | SHALIMAR BAGH | SHAKUR BASTI | TRI NAGAR | WAZIRPUR | MODEL TOWN | SADAR BAZAR | CHANDNI CHOWK | MATIA MAHAL | BALLIMARAN | KAROL BAGH | PATEL NAGAR | MOTI NAGAR| MADIPUR | RAJOURI GARDEN | HARI NAGAR | TILAK NAGAR | JANAKPURI | VIKASPURI | UTTAM NAGAR | DWARKA | MATIALA | NAJAFGARH | BIJWASAN | PALAM | DELHI CANTT | RAJINDER NAGAR | NEW DELHI | JANGPURA | KASTURBA NAGAR | MALVIYA NAGAR | R K PURAM | MEHRAULI | CHHATARPUR | DEOLI | AMBEDKAR NAGAR | SANGAM VIHAR | GREATER KAILASH | KALKAJI | TUGHLAKABAD | BADARPUR | OKHLA | TRILOKPURI | KONDLI | PATPARGANJ | LAXMI NAGAR | VISHWAS NAGAR | KRISHNA NAGAR | GANDHI NAGAR | SHAHDARA | SEEMA PURI | ROHTAS NAGAR | SEELAMPUR | GHONDA | BABARPUR | GOKALPUR | MUSTAFABAD | KARAWAL NAGAR | GURUGRAM | NOIDA | FARIDABAD
Craw Cyber Security (Saket and Laxmi Nagar) is just a few kilometer’s drive from these locations.
Can we help you?